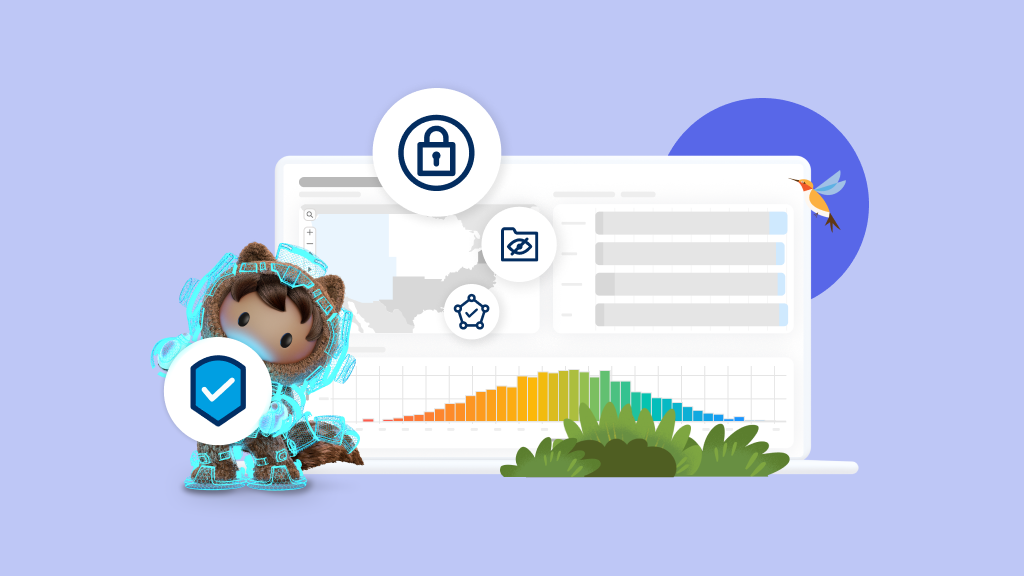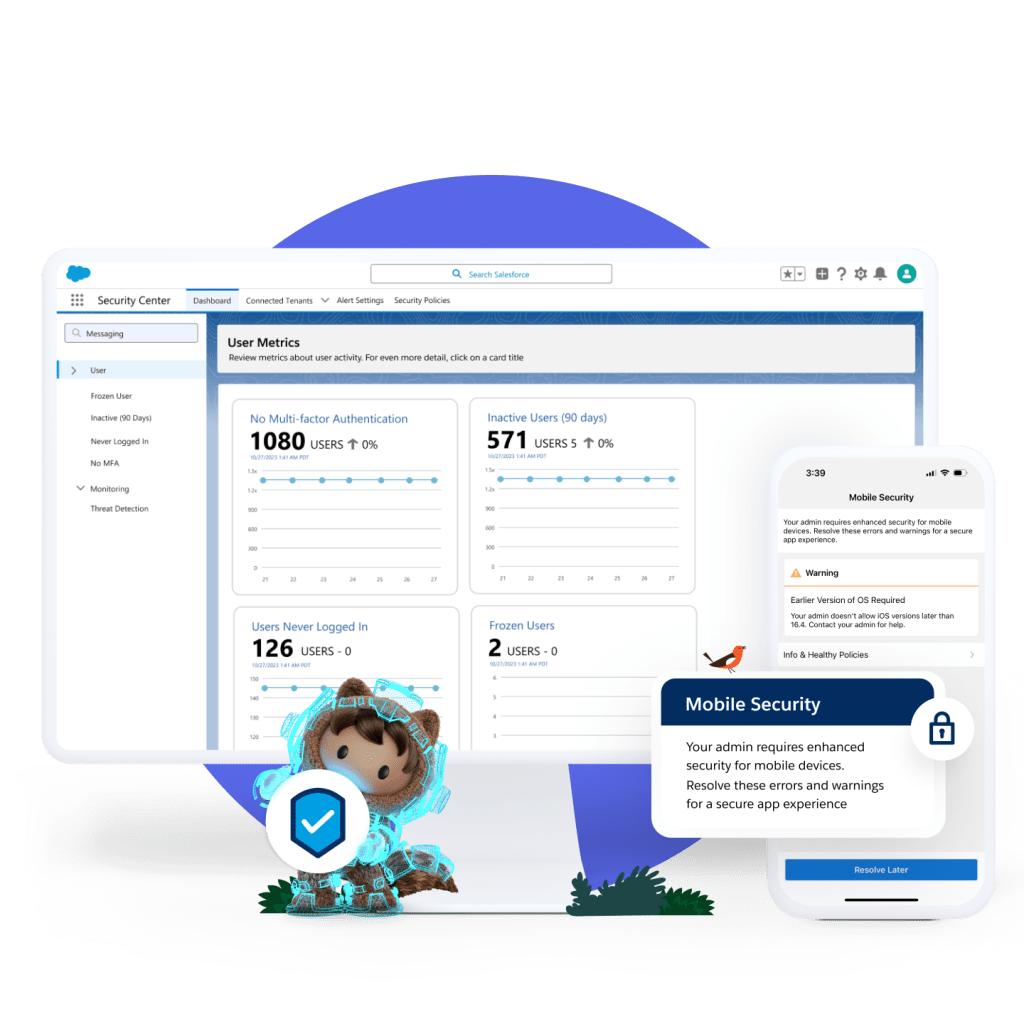
Data Security
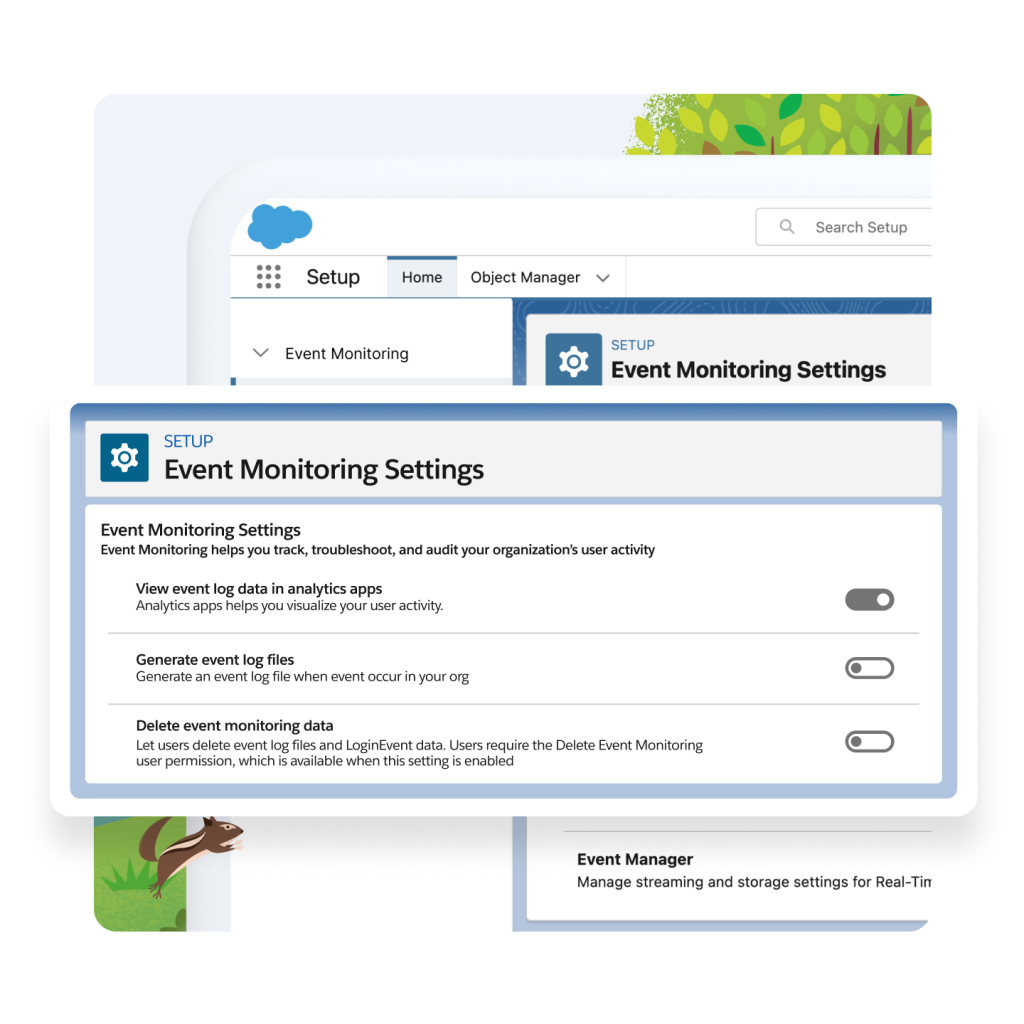
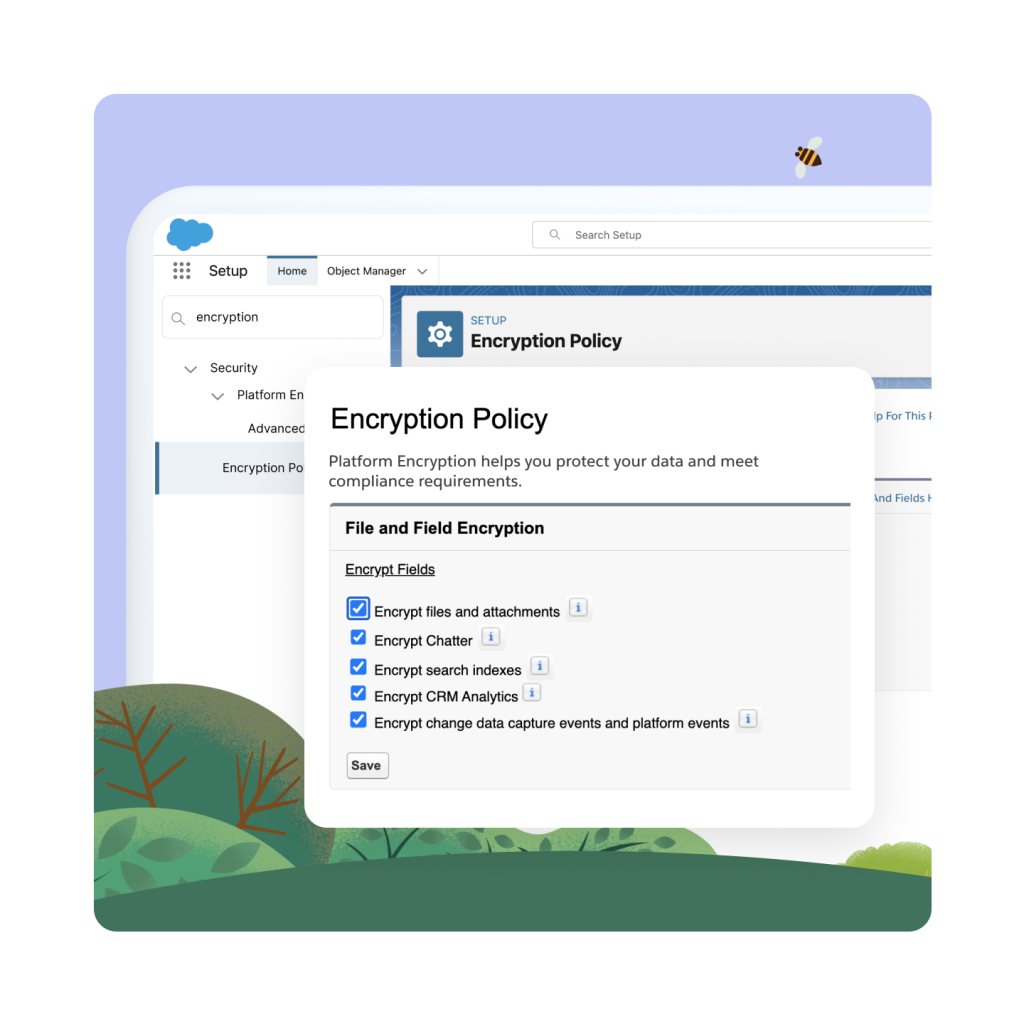
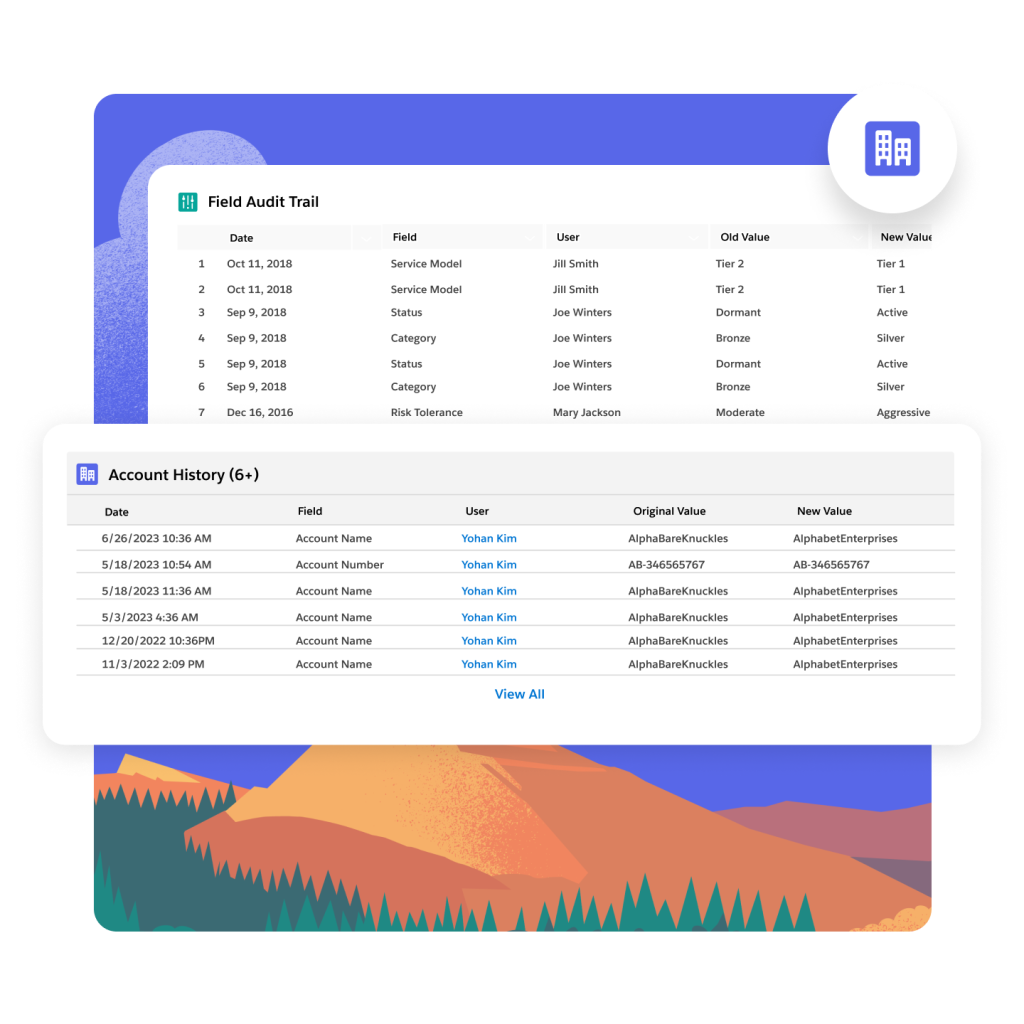
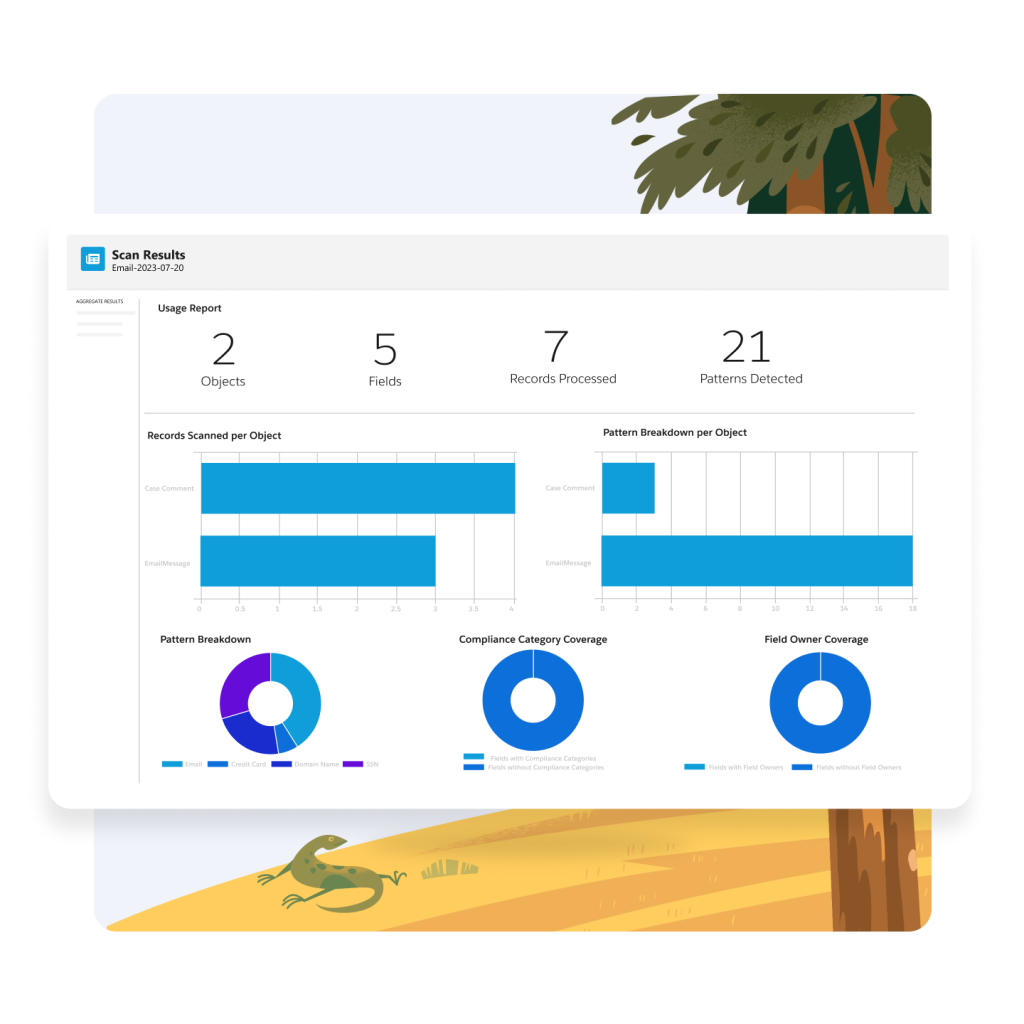
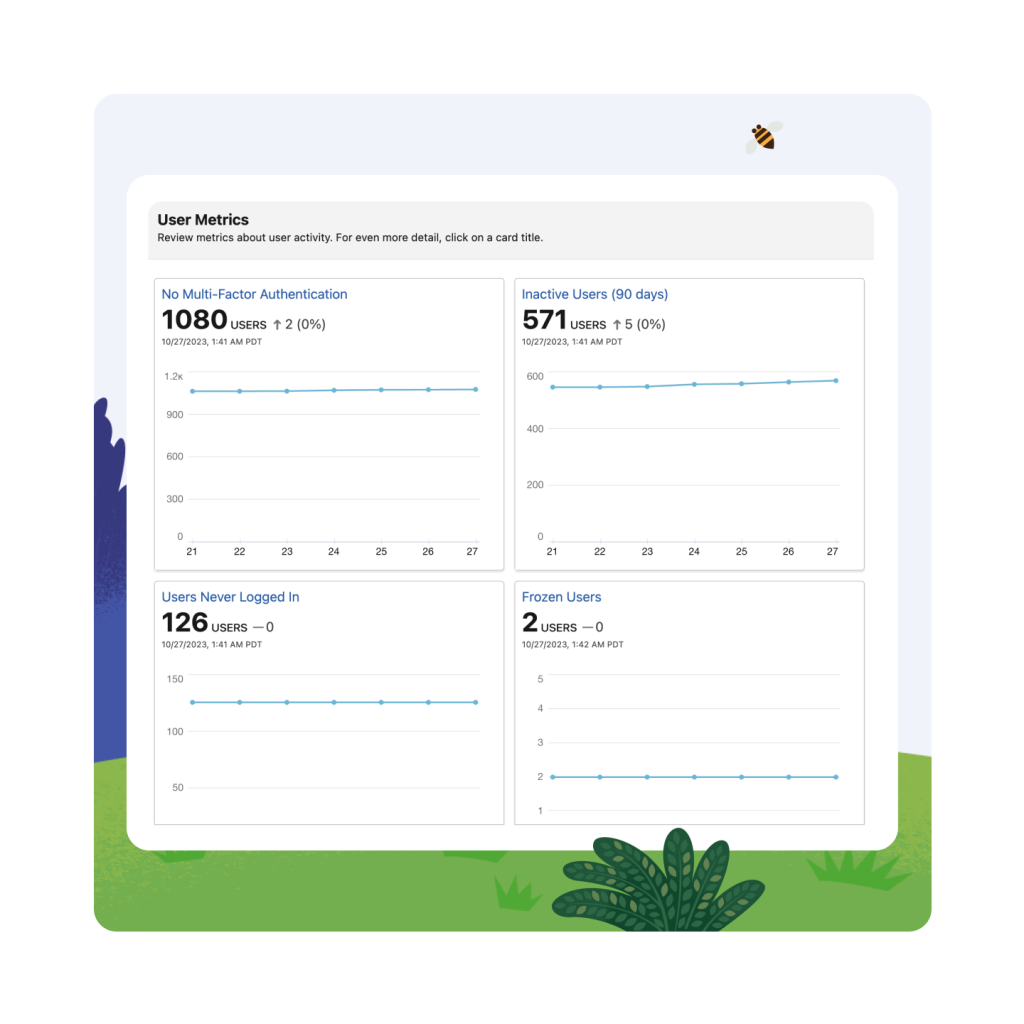
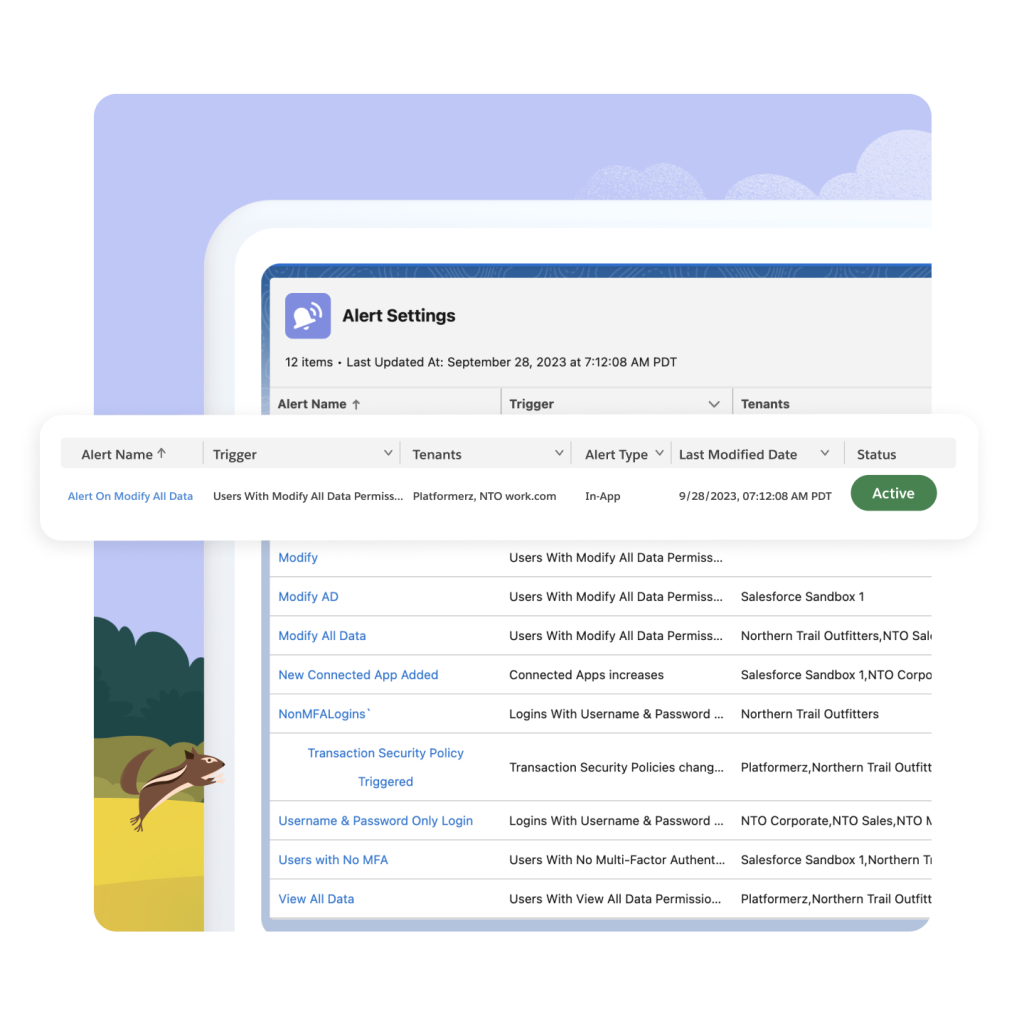
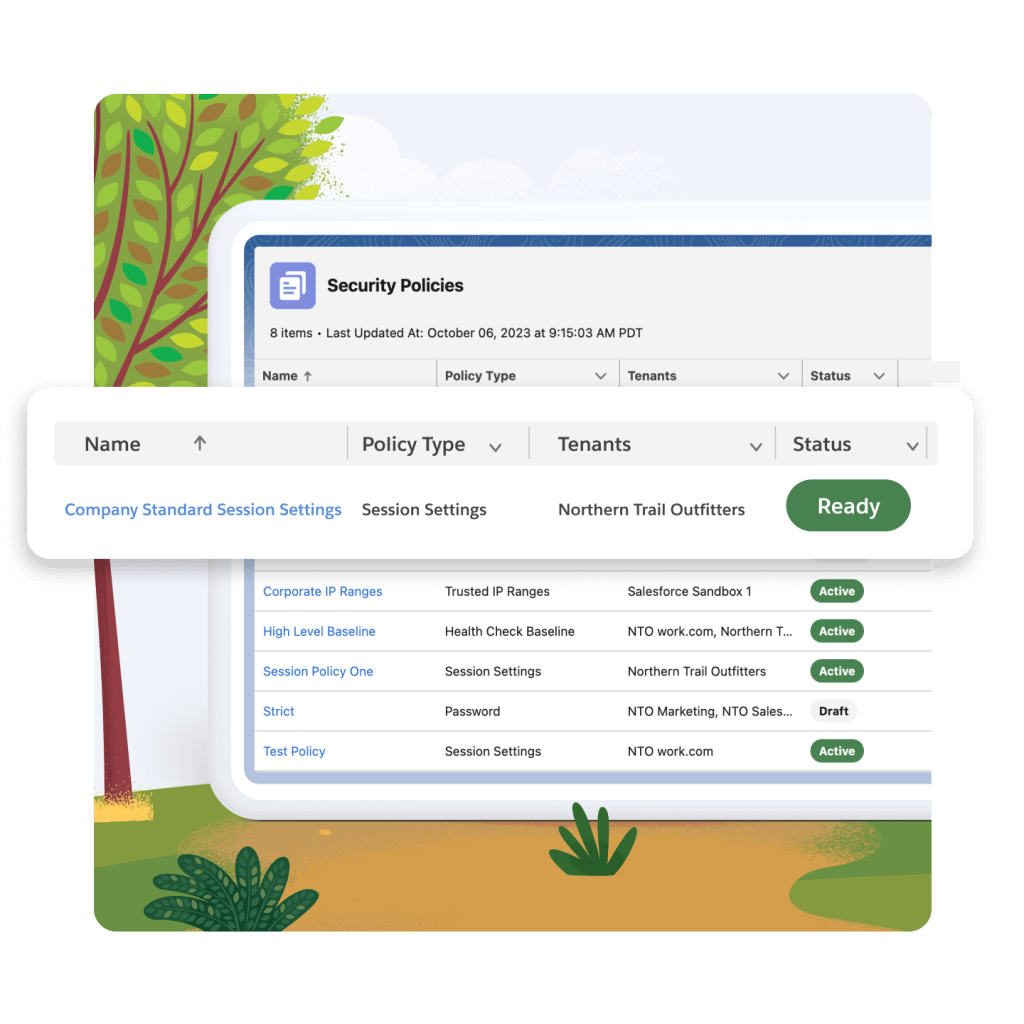
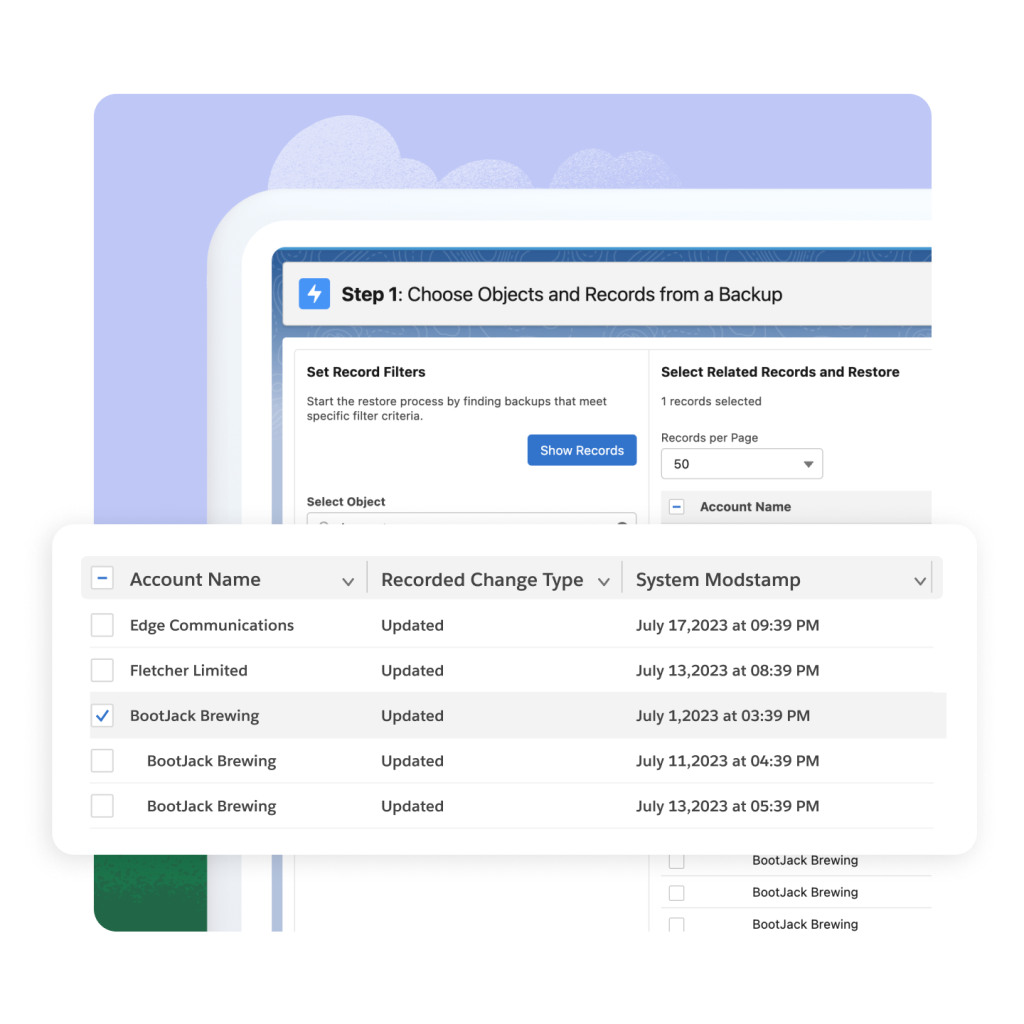
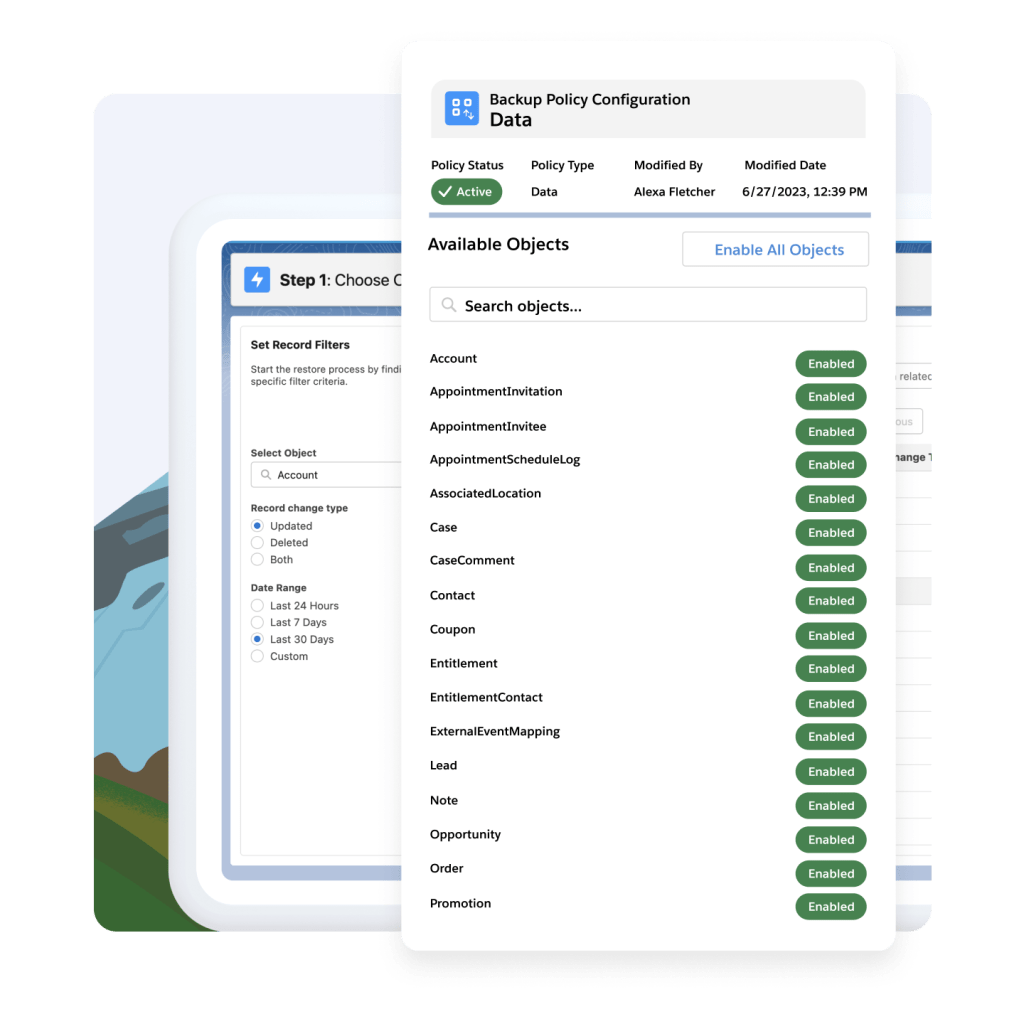
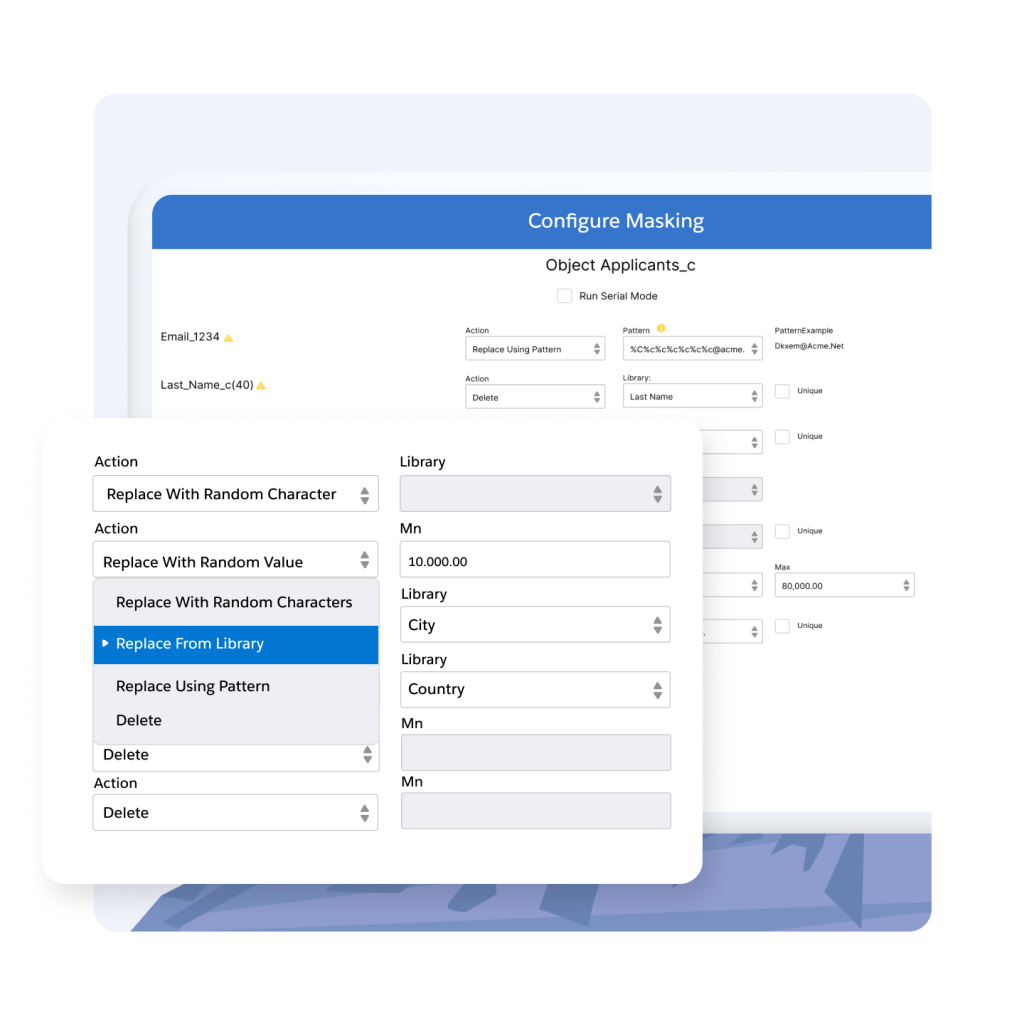
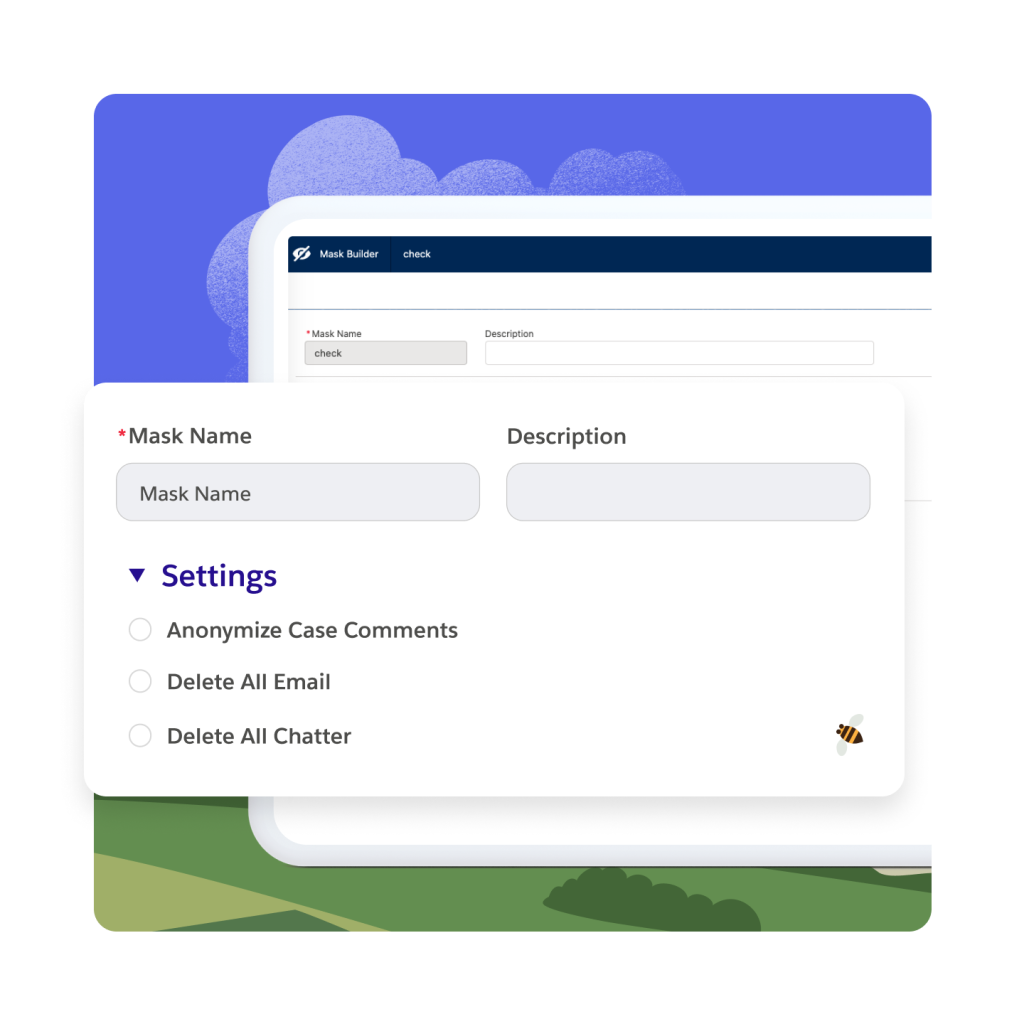
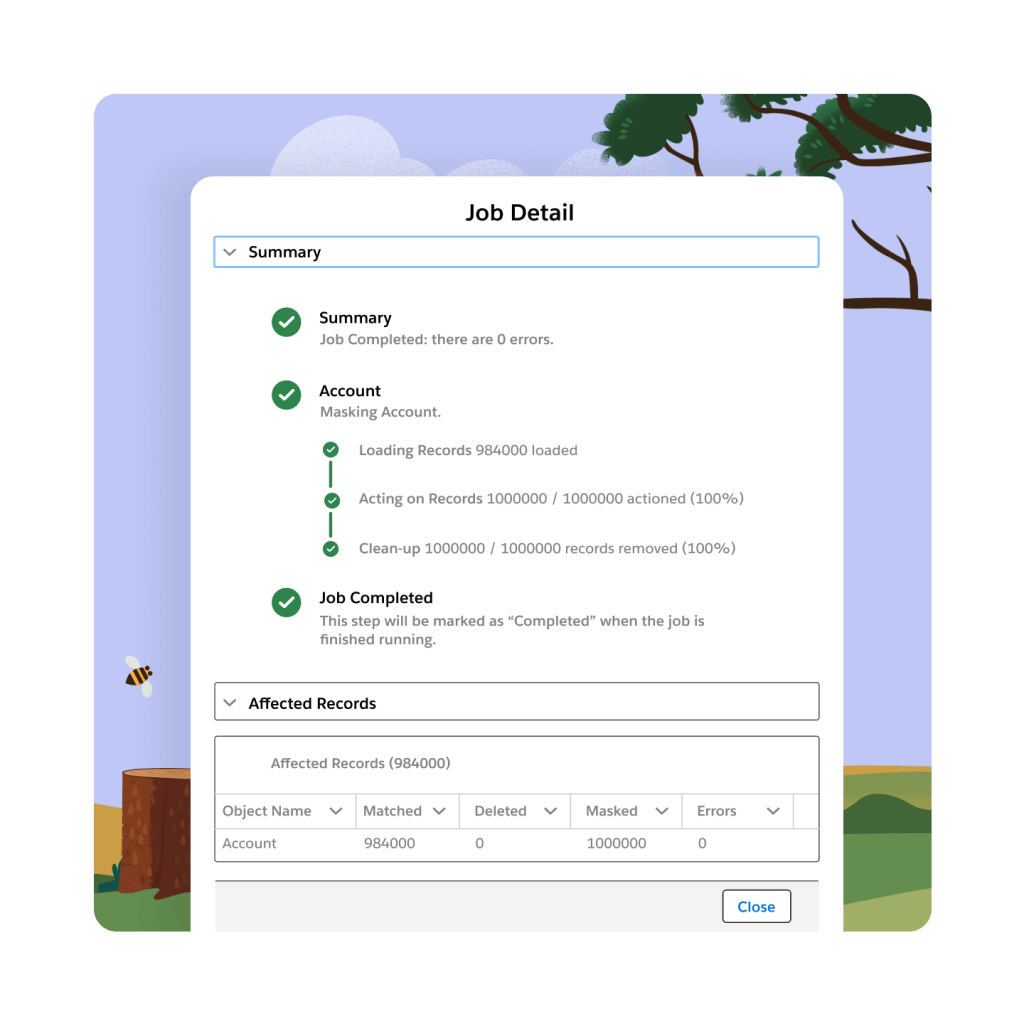
Minimize business disruptions while maintaining AI readiness with encryption, tracking of changes, and quick identification and classification of sensitive data. Effortlessly monitor permissions across multiple organizations, create and restore backups in the event of errors, and reinforce resilience against threats.