IT asset management covers more than just tracking devices or licenses. It’s a set of connected practices that help you manage cost, risk, performance, and compliance across your entire technology landscape, especially as you work through common ITSM challenges that impact visibility and control. Most businesses organize ITAM into four primary types, each addressing a distinct part of the asset lifecycle and service ecosystem.
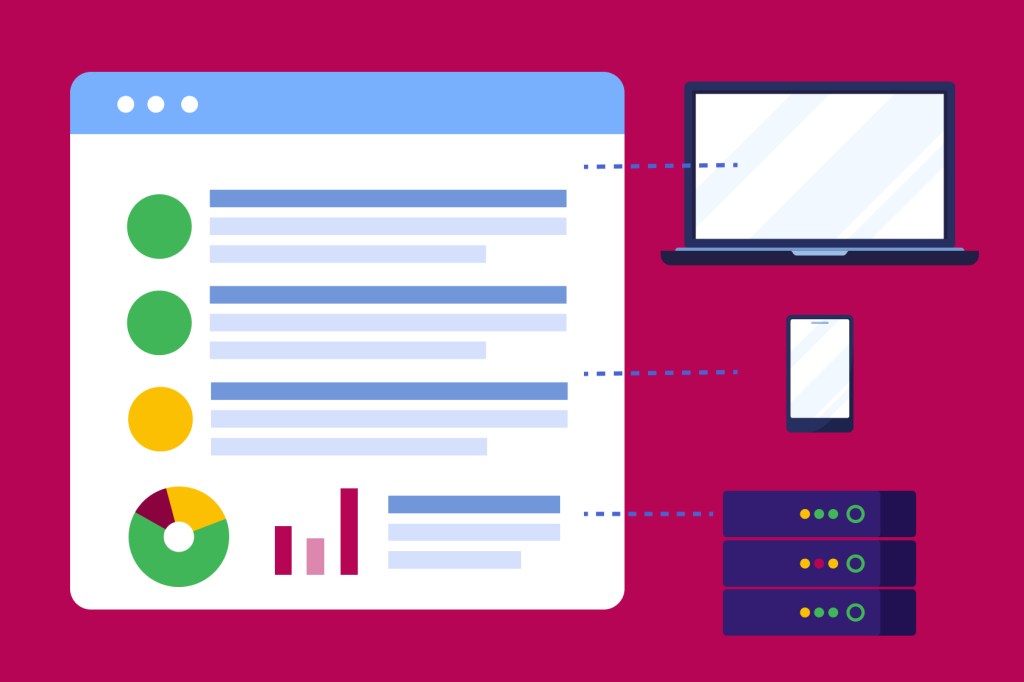
Hardware asset management focuses on physical equipment such as laptops, desktops, servers, and network devices. It gives you visibility into where assets are located, who is responsible for them, how they are performing, and when they should be repaired or replaced. With this level of control, you can reduce asset loss, improve refresh planning, support remote and mobile workforces, and maintain accurate inventory records.
Software asset management manages applications, licenses, subscriptions, and entitlements across on-premises and cloud environments. It helps you understand what software you own, what is actually being used, where compliance risks exist, and how renewals and contracts affect cost. Connecting software data to service workflows lets you eliminate shelfware, avoid audit surprises, plan renewals proactively, and align software spend with business priorities.
Cloud asset management extends ITAM into dynamic environments where resources scale automatically and costs fluctuate constantly. It tracks virtual machines, SaaS tools, platform services, and consumption-based resources so you can monitor usage patterns, allocate costs accurately, manage security exposure, and maintain governance without slowing teams down. This visibility becomes increasingly important as intelligent automation and autonomous agents, like Agentforce, interact directly with cloud infrastructure.
Digital and configuration asset management links assets to how services are delivered and supported. These assets represent configuration items, dependencies, integrations, and service relationships that connect technology to business outcomes. Maintaining this context lets you assess incident impact, manage change risk, coordinate problem resolution, and support ITSM best practices.